I worry about internet security for my home office or business what do I do?
This isn't meant to be an all inclusive guide to perimeter or firewall security, but if you worry about the security of your home, home office, or small business internet. Here's a great tip to use your cellphone as an infosec tool to assess the security of your perimeter. So let's dive right in:
- From a computer on the network you'd like to test go to whatismyip.com
- Take note of the IPV4 address, this what we call your real world IP address we're going to need it in the next step.
- Download Fing from the android or iOS app store.
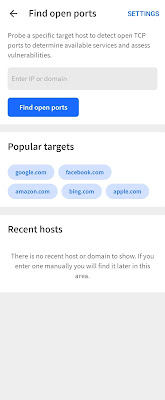
- Open Fing Click Tools at the bottom then click "Find open ports" Input the IP you got from step 2.
- Before you click scan make sure to turn the Wi-Fi off on your device, you want to simulate an external scan of your network, and your cellphone disconnected from Wi-Fi does a good enough job of representing that for a quick and dirty test like this.
- The results will identify different ports and services, sometimes with a short description or explanation of what the service related to the part does. Here are just a few to watch out for especially if you don't have a reason for these services to be available outside of your home or office but if you do I would maybe reconsider using a VPN to access these services:
- 80, 8080, 443: Usually used for web based control panels for routers and other networking and inter-faceless equipment.
- 3389, 5900: Remote desktop ports for Windows and VNC (Mac/Linux/Windows)
- 137, 138, 139, 445: These ports are found in Windows Networking and File Sharing
- 548: Apple Filesharing Protocol
- 22: SSH used to remote manage and control computers.
- If you find a port that I didn't list google: what does x port do? to find your answer.
- Careful I just taught you how to port scan so now you have to promise to only do it to things you own or you could get in serious trouble.


Comments
Post a Comment